If your phone suddenly loses the ability to place calls or send and receive texts, you may be victim of a cyber crime. Whether you call it SIM hijacking, SIM jacking (simjacking) or SIM swapping, it’s on the rise. And it gives cyber criminals the chance to drain your bank account, access PHI on your business servers and more.
SIM hijacking, like all forms of cybercrime, is becoming more common. The changes to how people live and work because of COVID-19 has made cyber attacks easier. No doubt, job losses and unstable economies around the world have also increased the number of people tempted by the potential income of cybercrime.
SIM Cards and SIM Hijacking
If you’ve ever bought a smartphone, you’ve probably heard of SIM cards. They are small chips that hold all the data your phone needs to identify to your mobile carrier that this is your phone. Think of it like the phone’s social security number. It tells your carrier where to direct your phone calls, text messages and any other data sent over your cellular connection.
SIM hijacking happens when a cyber criminal takes over your SIM, routing your calls and texts to their device instead of yours. Your phone? It will still be able to connect to Wifi to run apps and games, but no calls or SMS text.
Unlike what the term “hijacking” implies, the cyber thief doesn’t need to come anywhere near you to hijack your SIM. It can be done from another city, or even another country. The physical SIM card never leaves your phone.
Instead, the criminal impersonates you using information gathered through social media, the dark web or previously stolen from you with tactics like phishing. The hacker just needs enough information to convince one person at your mobile carrier that they are you. Then they request the SIM be transferred to another device.
How Hijackers Use Your SIM
Once your calls and texts are going to the hijacker’s device, he or she will start trying to access your accounts; typically starting with banks and credit cards. Having your SIM helps because when you login from a new device, accounts often send a text or call to verify it is you. With your SIM coming to their device, hijackers are able gain access.
Signs Your SIM May Be Hijacked
The most obvious sign of SIM hijacking is that your phone can no longer make or receive calls or SMS text messages (messages through wifi-based texting apps like Facebook Messenger or What’s App will still work). Depending on your carrier, you may also receive notification that your SIM is being used on another device. You may also notice posts made to your social media account that aren’t yours. Or you might be unable to access your accounts, like your bank account and credit cards.
Suspect SIM Hijacking? Here’s What to Do
Call your bank and phone carrier immediately. You may be able to stop the hijackers from getting any further or doing too much damage. If you are an Aeko client, call us as well. Our data experts can work to prevent hijackers from using the SIM to access your business network. It can’t hurt to take steps to secure your social security number, credit cars and other information. Visit IdentityTheft.gov for a complete guide.
SIM Hijacking Prevention Tip #1: Use An Authenticator App
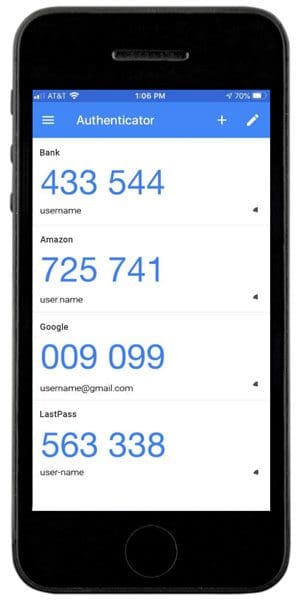
Multi-factor authentication (MFA) comes in many forms. The two-factor authentication that sends text messages and calls is one of the earliest adopted forms of MFA. It’s more secure than not having MFA, but has that Achilles heel of SIM hijacking.
Multi-factor authentication by app has no such weakness. Instead of the account pushing out a code to you by a phone call, text or even email, you already have the code you need in an app on your phone. Learn more about MFA.
SIM Hijacking Prevention Tip #2: Password Hygiene
COVID-19 has made us all more conscious of good hygiene. Apply that to your passwords as well. Here are some password dos and don’ts:
- Do change your passwords. NOW. If you are like most people, you’ve been using the same password since you opened those accounts. Start with your bank account and mobile carrier.
- Don’t use the same password for multiple accounts.
- Do use a password bank, like LastPass to securely manage your passwords. (HINT: your browser “remember” feature is not secure.)
- Don’t include any part of your name or birthdate in your passwords.
- Do use multiple character types, even if they are not required by the platform. That means using UPPERCASE and lowercase letters, numbers and at least one special character.
For your mobile carrier, you can request that they require additional (different) password or PIN code to make any changes to your account. With the rise of SIM hijacking, more and more carriers are giving customers this option, but you have to ask for it.
SIM Hijacking Prevention Tip #3: A Good Offense
If you are a business owner or employer, share this information with your staff. It can help your team avoid falling into traps and better secure their accounts. Of course, SIM hijacking is one of many tactics cybercriminals use to attack individuals and businesses. The best defense is strong IT infrastructure and a comprehensive cybersecurity plan for your business.
Need help? Have a question about cybersecurity for your business? Contact us.
Are you aware of the most common cyberattack methods?
Did you know there are over 3.4 billion phishing emails sent every day? Phishing and other cybercriminal behavior are a lot more common than you’d think.
Our free “Phishing, Smishing, Vishing, Pharming? A Cyberattacks Guide” will inform you about cyberattack methods and give you the latest in data security tips.