Aeko Technologies Downloads
Whether you’re thinking about which IT support provider to choose, evaluating your cyber security needs, or want to examine phishing prevention, we’ve got you covered.
How strong are your business’s passwords?
Weak passwords are surprisingly easy to come across. Were you aware that 81 percent of hacking-related breaches used stolen or weak passwords?
Our free Super Simple Password Management Guide will give you the best password management tips to secure your business.
Are your employees using AI the right way?
Protect Your Business
Picture this: with a rock-solid artificial intelligence policy in place, you're not just safeguarding data and beefing up security – you're protecting your assets and ensuring business continuity.
Avoid accidental AI blunders and ethical concerns. Our Artificial Intelligence Policy Template can guide you and your company through the digital wilderness with clarity and responsibility.
Want to take the guesswork out of comparing IT providers?
Download the IT Planning Cheat Sheet
- Clarify your current IT services needs.
- Express your company’s future goals.
- Compare MSP and IT service providers.
- Feel confident and prepared when interviewing potential providers.
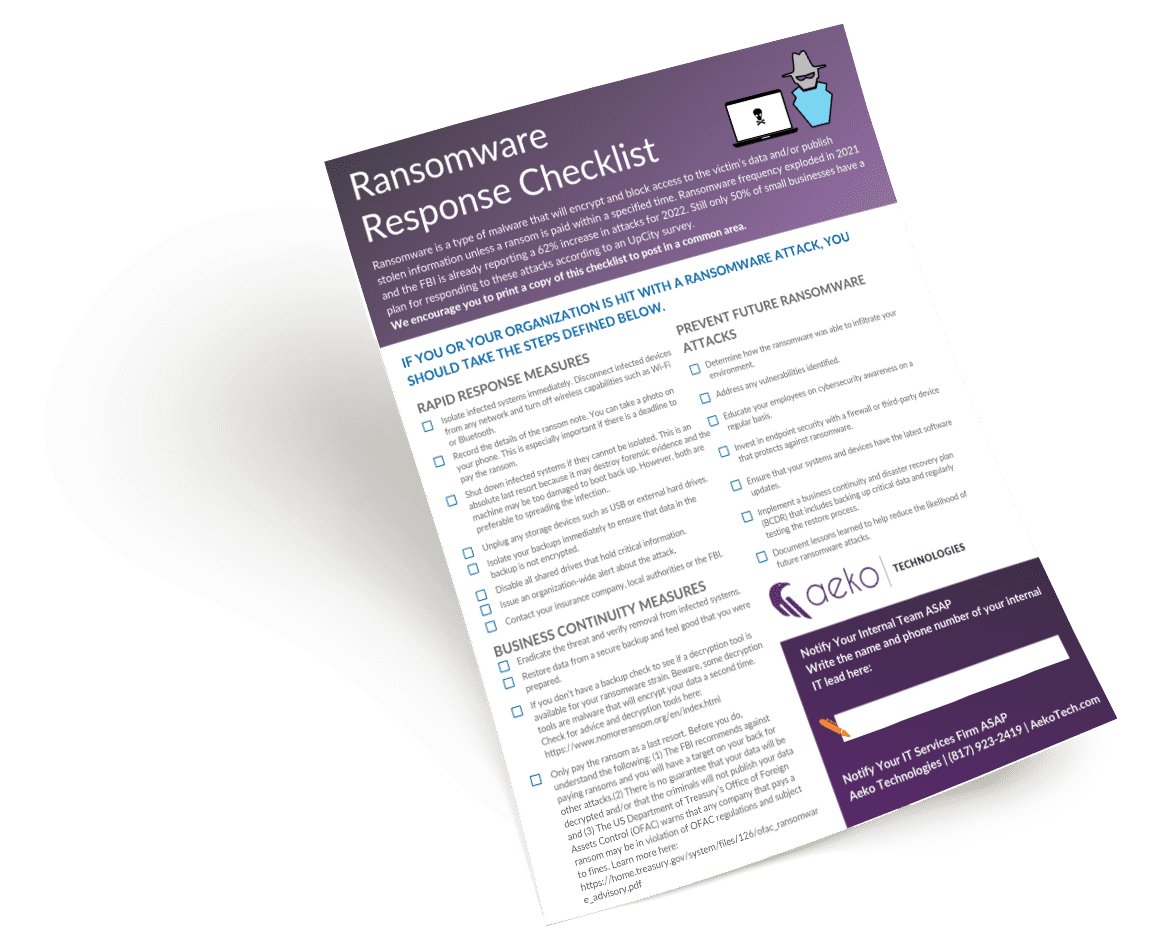
Concerned about ransomware attacks?
Download the Ransomware Response Checklist
This checklist guides your team to a resolution quickly and confidently. It includes:
- Ways to respond.
- How to eliminate the threat and get back to business as usual.
- Steps to prevent future ransomware attacks.
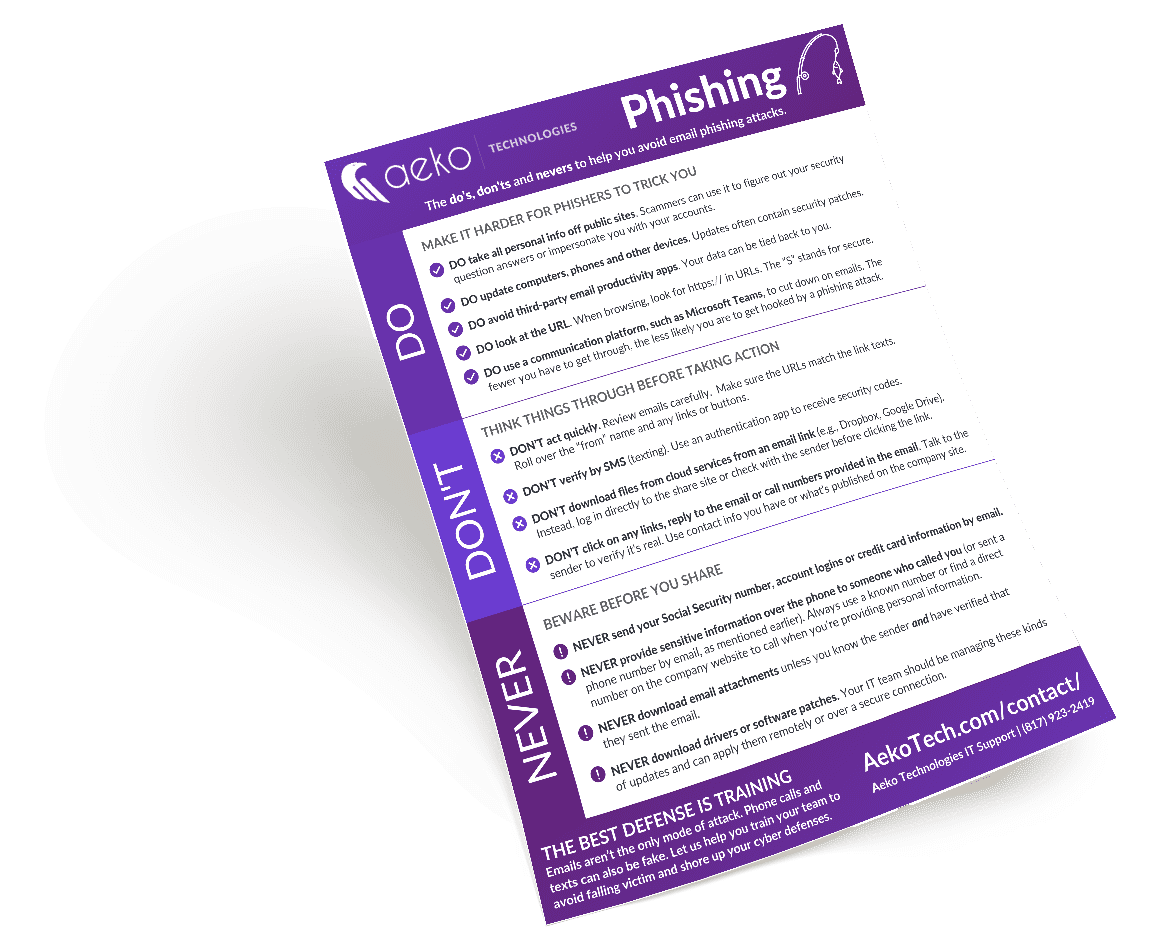
Can your team spot “phishy” emails?
Download the Phishing Prevention Cheat Sheet
When it comes to phishing, training is the key to preventing a breach. This cheat sheet is a great way to remind your team of the DO's, DON'Ts and NEVERs of email safety.
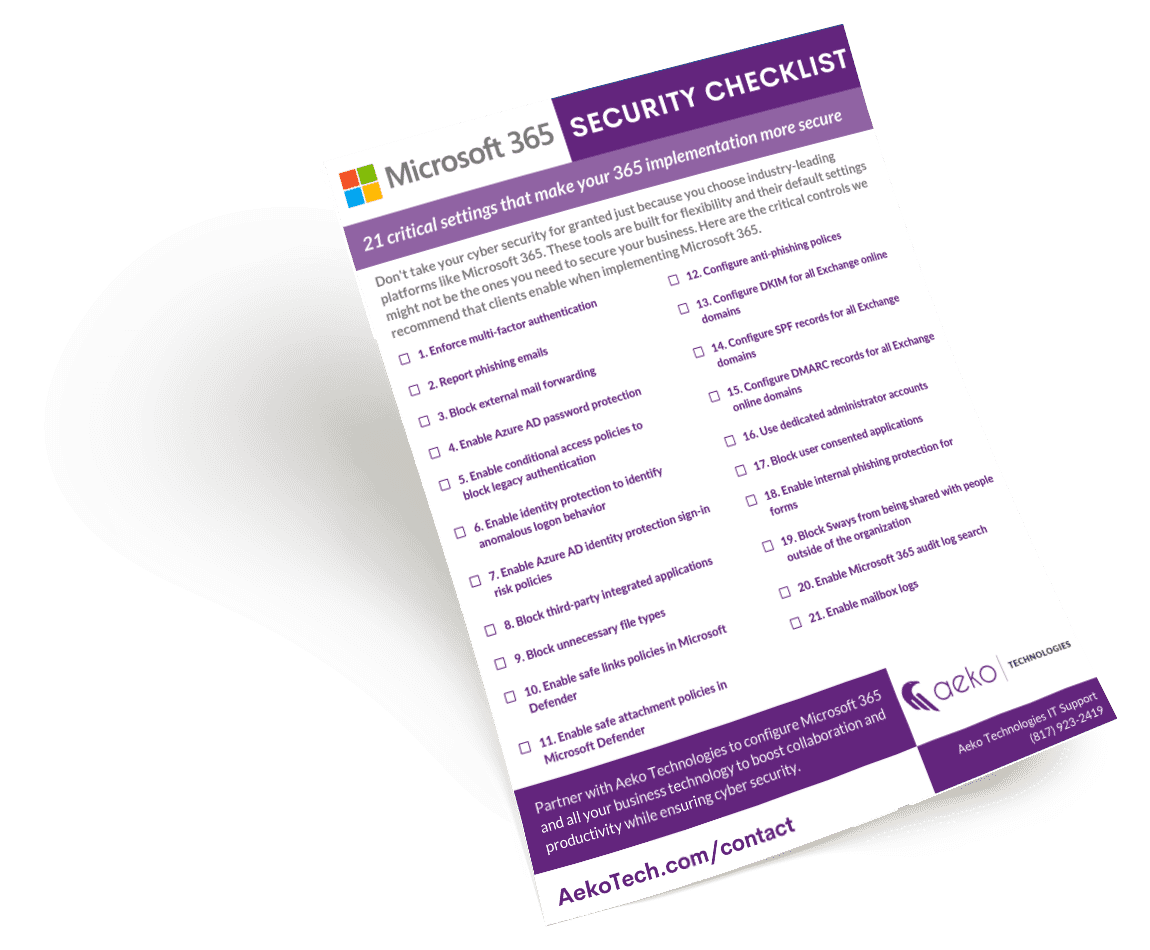
Is your Data Safe in the Cloud?
Download the Microsoft 365 Security Checklist
This simple and easy checklist outlines the 21 critical settings you need to have for a secure MS 365 environment.
How protected is your business?
Download the Phishing, Smishing, Vishing Cyberattacks Guide
Did you know that a new phishing website is created every 20 seconds and that over 3.4 billion malicious emails are sent out every day? Cybercrime is on the rise: The only question is, can you identify it before you become a victim?
Our free guide will give you the tools you need to be better informed on cybercrime. Secure your business today.
Is Your Fort Worth Business Secure?
Download the Cyber Security Essentials Checklist
- Take control of all endpoints connected to your network.
- Minimize opportunities for attackers.
- Improve your ability to detect social engineering attacks.
- Create a DBR plan so you’re prepared if an incident occurs.
- Defend your network against security threats.
- Refine and review your vendors to protect your data and save money.
- And more!
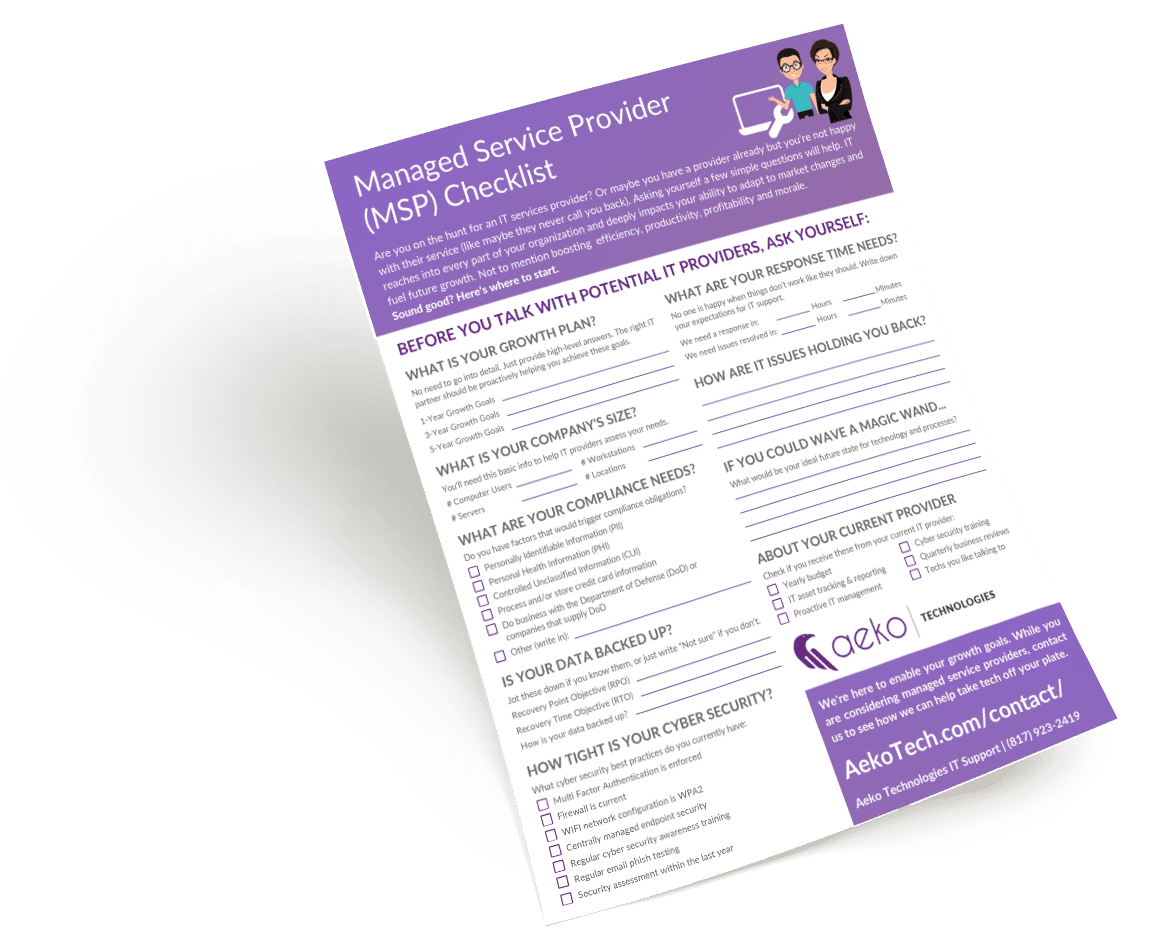
Are you ready to choose IT support, but don’t know where to start?
Download the Choose IT Support Checklist
- The stats potential MSPs will need to assess your needs.
- Business areas that might lead to compliance needs.
- Your backup and disaster recovery objectives.
- Your current cyber security tools and practices.
- Your IT support expectations.
Aeko Technologies Downloads
FAQ
Have any other business IT questions? Check out our FAQ page for more information on everything from project outsourcing to what a managed service provider can do and everything in between.
The Cleared-for-Takeoff Blog
Discover the latest IT solutions news, tips and stories of businesses reaching new heights exclusively at our professionally curated blog.