It Compliance Services to Keep Your Paperwork Straight
You don’t want your business to fall off course when it comes to regulatory compliance rules.
Charting Your Route to Compliance
Meeting compliance standards is critical for your business. Large or small, organizations that deal with certain kinds of information need to follow regulations to the letter. Being non-compliant can jeopardize your company’s reputation. It can prevent you from doing business with certain government agencies or within certain markets. It can cost you time and money in reporting, fines and possible lost revenue.
The Aeko Technologies team understands today’s regulatory needs and is always watching for changes in the landscape.
Don’t risk failing an audit! Count on our proven systems for protecting data... and easing your mind.
Aeko’s knowledge of control and compliance comes from years of experience with Sarbanes-Oxley (SOX) regulations for an S&P 500 company.

CMMC Compliance: The Time Is Now
If you are doing business with the Department of Defense (DoD), Cybersecurity Maturity Model Certification (CMMC) is now the law of the land. Gone is the easy method of self-certifying through NIST 800-171 cybersecurity framework. The goal of the switch to CMMC is to deter breaches and avoid disruptions in the supply chain.
As part of CMMC, your business will be audited to ensure IT compliance with one of five regulatory levels. Choosing the right level for your organization is critical to passing this audit.
Aeko Technologies helps companies meet CMMC regulations, choose the right level, prepare for an audit and more. Learn more about how the new CMMC process works and what you need to be successful. Or book an appointment for a free consultation.
Credit Card or PCI Compliance
Credit card (or PCI) compliance is changing, too. Many companies are feeling the effects of recent tightening of requirements by credit card (CC) processors. According to PCI Security Standards Council, more changes are on the way: The current proposed timeline puts the PCI DSS 4.0 to be completed in mid 2021.
With Aeko’s comprehensive PCI assessment and tools, we provide clear reports based on where you are today. These reports outline your short- and long-term goals for meeting PCI compliance.
Don’t risk failing compliance checks or being blindsided by CC processor changes. Call on our team to help your IT department or to take IT compliance concerns off your to-do list completely.
HIPAA Compliance
With support from the Aeko team, you can meet HIPAA regulations and get back to business.
With Aeko’s efficient HIPAA assessment and tools, we thoroughly document your organization’s current situation. Our reports help you build a tactical technology strategy for both short- and long-term goals. Book an appointment for a free consultation.
Your IT Compliance Questions, Answered
What is a compliance service in information technology?
What are compliance activities?
What is the difference between compliance and security?
What are the different types of compliance?
What is the goal of compliance?
What are the risks of noncompliance?
Is Cyber Insurance Worth the Investment?
Today, when data is king and cyber threats loom around every corner, the question “Is cyber insurance worth the investment?” is more relevant than ever. The stakes are high, and a single breach can result in catastrophic financial and reputational damage. To shed light on this pressing matter, we turn to the case of the…
Read MoreHIPAA Compliance Support
As a solo practitioner or larger healthcare and medical provider, HIPAA compliance support is critical to your practice’s success. You’re well aware that failure to comply with the Health Insurance Portability and Accountability Act (HIPAA) can translate to fines and reputational damage, which is why we’re here to help. Safeguarding Your People and Data Are…
Read More5 Ways to Limit IT Liability With Field Technicians
Field technicians are essential to providing IT support, but they also introduce an IT liability to your infrastructure. This is an emerging threat as there are more and more endpoints to manage and secure. In this article, we’ll outline five ways to limit your IT liability while allowing field technicians to do their job. Endpoint…
Read MoreProtect Your Cloud Data
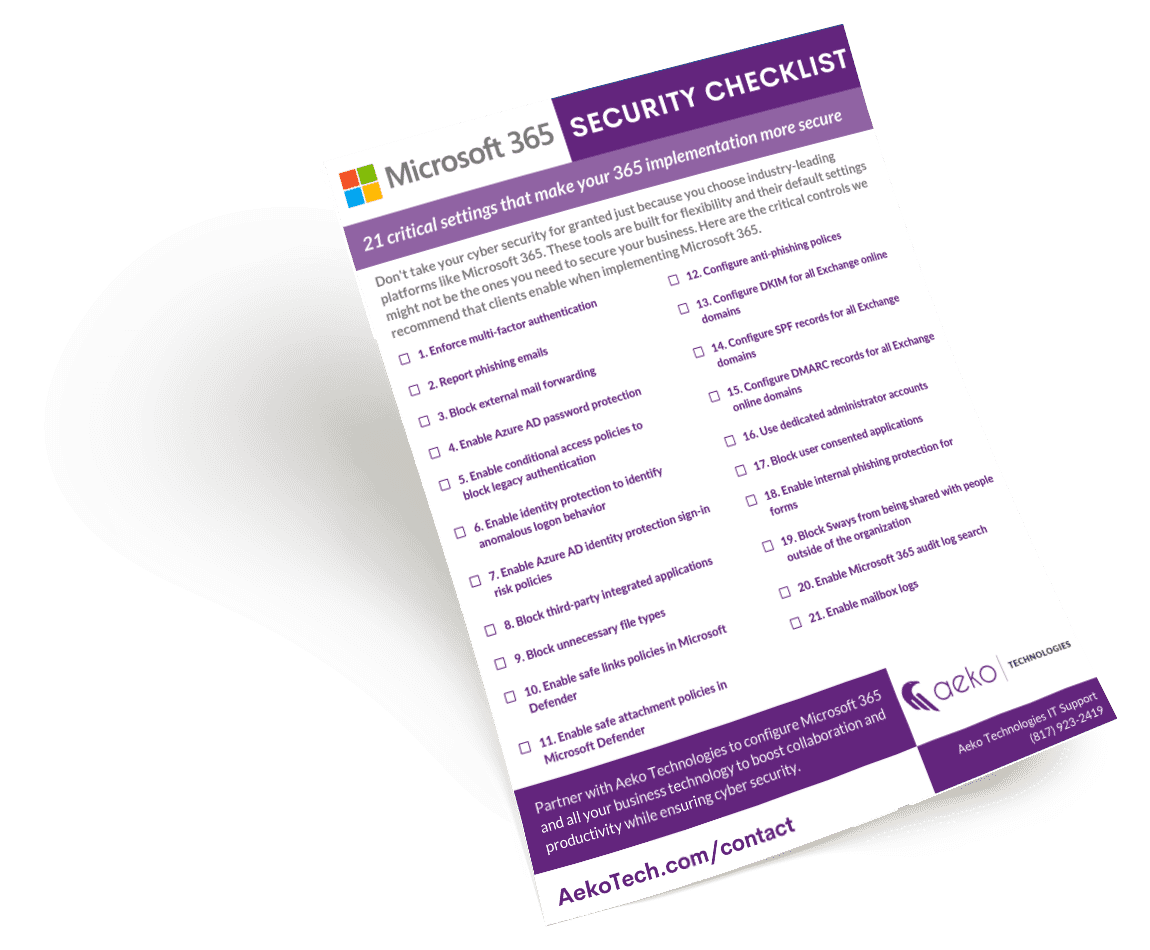
Don’t go into a cloud services agreement with blind trust. Just because it is on the cloud, doesn’t mean it is safe. Get the 21 critical settings you need for Microsoft 365 security.
Download Now
We support a variety of industries throughout the Forth Worth and Dallas regions. Every industry has its own ways of working. Aeko understands the customs and quirks of your field so we can hit the ground running. Learn about our experience providing IT outsourcing and services in your industry.